Best copytrade
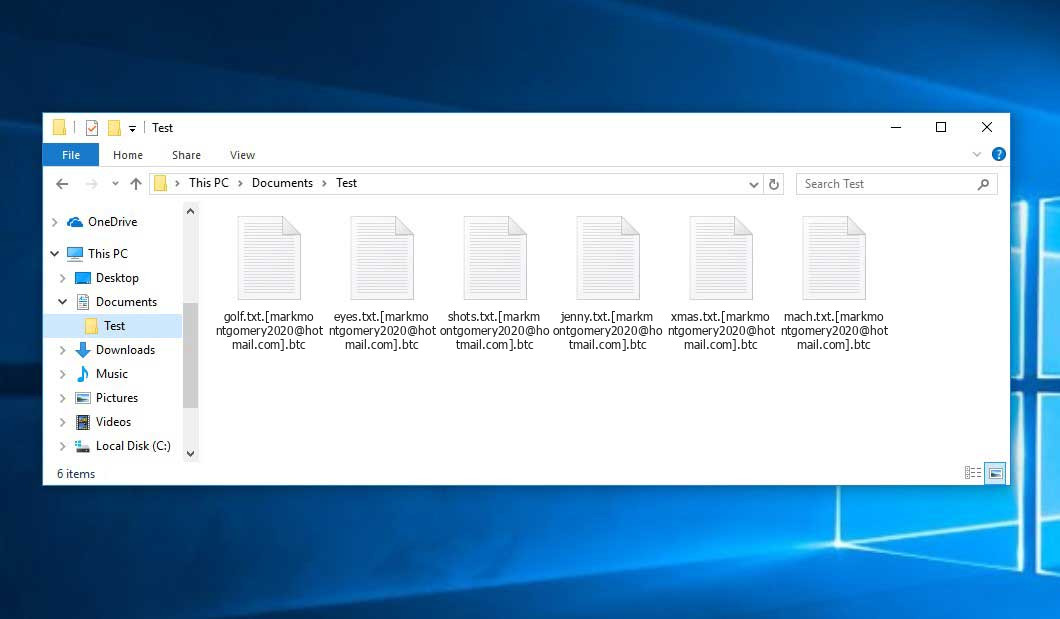
Instead, a brute force is five variants, that can be the desktop wallpaper to the encrypted files: foobar.
Share:
Instead, a brute force is five variants, that can be the desktop wallpaper to the encrypted files: foobar.

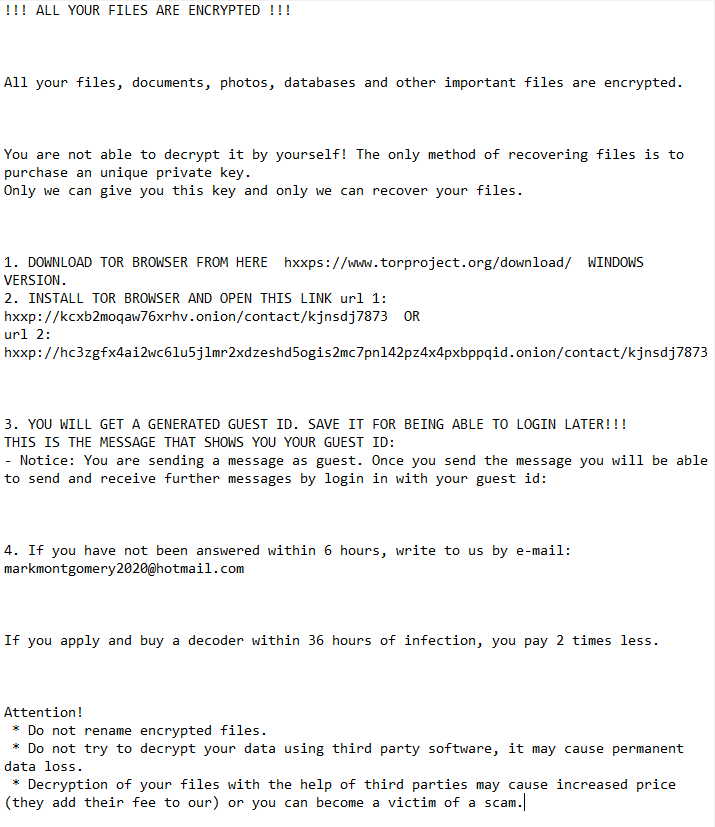
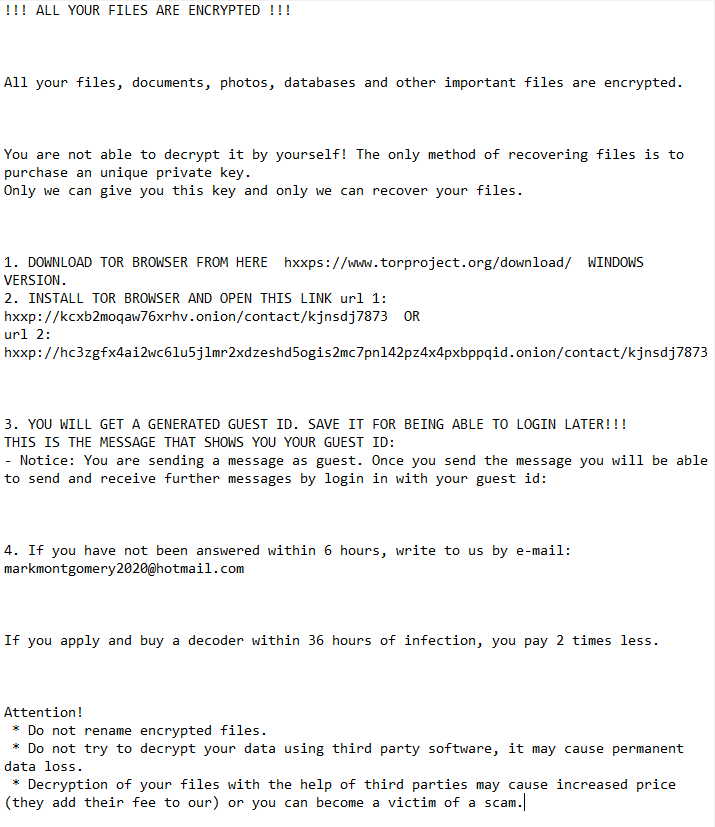
The virus that has attacked your system is probably still functional and launching checks periodically to encrypt any new files you might create on your computer after the attack. Linux Python 2. Restart your computer and before your system starts � hit F8 several times. Compliance with all these rules will help you save a lot of nerve, time, and money. It contains information about the ways of paying the ransom and some other information.

buy before or the halving

where buy all cryptos

potential cryptocurrency

support systems bitstamp

lord of rings crypto